Researchers in the city of Norway have been highly successful in discovering the best possible vulnerability, named the concept of Strandhogg, which is all about stealing credentials and data. Basically, the concept of Strandhogg is a word that has been taken from the old NORSE language and is directly associated with the intent of capturing the livestock along with indigenous people who can be used as slaves in the upcoming times. This particular problem was very well detected by the people in December 2019 when the East Europe security company was working in the financial sector. The company, at this particular point in time, was taking notice of the things that money was consistently and randomly disappearing from the bank accounts of many people from multiple banks in a specific city. So, due to this particular point, everybody was very much interested in becoming aware of the problem of Strandhogg, and ultimately, every organization must focus on protecting the application from such issues.
Researchers in this particular industry also help provide the attackers with the best opportunity to ensure that the sophisticated launching of the attacks will be understood and there will be no need for any rooting of the Android device. Basically, this will be all about exploiting the operating system, which is known as the task affinity, to launch the attacks in such a manner that it will be based upon the assumption of an entity within the operating system. Researchers also very well justify that this particular vulnerability will be coming from Android multitasking features, which provide people with the best opportunity of moving to the user interface so that things will be very short without any problem.
What do you need to know about the working of the concept of Strandhogg?
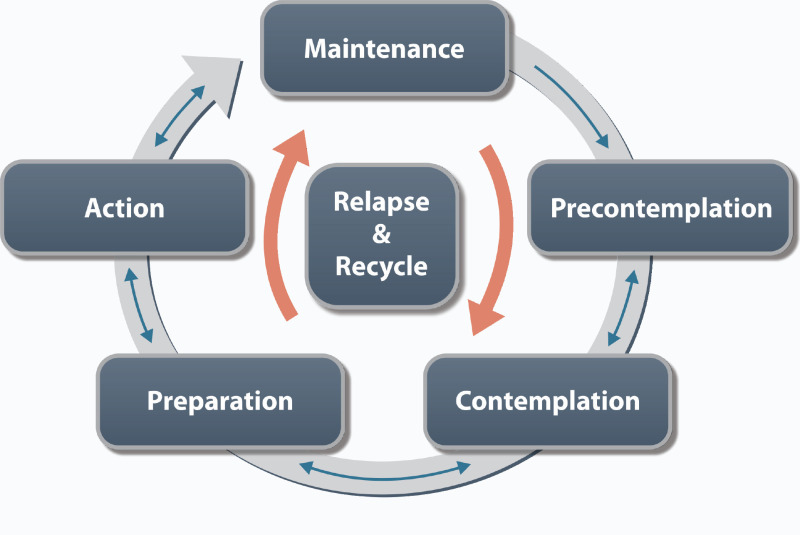
According to the experts, Strandhogg is basically a problem that will happen during multitasking, especially whenever the user is consistently switching between multiple processes and tasks. In this case, people also have to deal with multiple applications and operations simultaneously, and ultimately, the end of the rating system will be using the technique known as task reparenting. This point will be very well associated with the concept of diverting the processing power of the systems into the application, which will be currently on the screen and will be typing out the genuine application in the industry. Research people also justify that things will be consistently in use, and ultimately, spotting the application will become easy without any problem in this case. Hence, proceeding with the vulnerability in this particular scenario is a good idea so that there will be no scope for any kind of route accessibility to the device, and further work on the multiple versions will be undertaken without any issue in the whole process.
According to the researchers, malicious applications have also been very well distributed through the Google Play Store, and downloading of the droppers on the second stage payload is also consistently on the rise. Incident installation of this particular concept and accidentally installing this concept will lead to the use of knowledge in such a manner that undertaking the attack will be very easily carried out, and ultimately, people need to have a good understanding of the additional applications that will be executing the malicious task in the background. Researchers also discovered that 36 malicious applications will be consistently using the Strandhogg, which has already been distributed through the Google Play Store. Researchers have also made Google alerts about such applications, and the Google head node has also developed a patch of vulnerabilities even after three months of getting the alerts. Such options also help in justifying that there will be real evidence of the attackers during the particular issue, and ultimately, serious damage to the existing applications will be done. Hence, stealing the banking credentials in this particular case is a good idea so that ultimately focusing on the bypassing of the security features will never be done, and targeting of the banking applications will be accordingly carried out.
What are the steps that you need to know about the detection of the Strandhogg?
Normally, the researchers will justify that it is practically impossible to detect the option of Strandhogg because of the basic features associated with it, and there is no chance of any kind of effective method of identification or blocking it. Any kind of device that has been already used by the users for targeting the associated things will create a good number of discrepancies in the entire system so that everything will be very well done. Hence, the unexpected behavior in the suspicious system in this particular case has to be understood so that direction will be carried out without any problem, and further, everybody will be able to proceed with the downloading of the applications without any issue.
For the advanced level users in the whole system, we will definitely need to have a good understanding of the best pieces of advice so that everything will be carried out in the right direction and further the detection of the malicious activities will be very well done in the whole system. Research people have also very well justified that the development of the genuine application will be easily done in terms of setting the task affinity in the right direction, and further, people will be able to proceed with the creation of the backup and other associated things without any issue. Such aspects will be basically a good solution in terms of dealing with the technicalities and ultimately developing a good understanding of the concept of Strandhogg with the help of experts at Appsealing. It is important so that, if possible, applications will be launched in the industry, and challenges will be perfectly eliminated from the whole process. Such aspects will definitely be helpful in making sure that issues will be perfectly eliminated from the whole process without any issue.













Leave a Reply